23Dec-19
17Jul-19
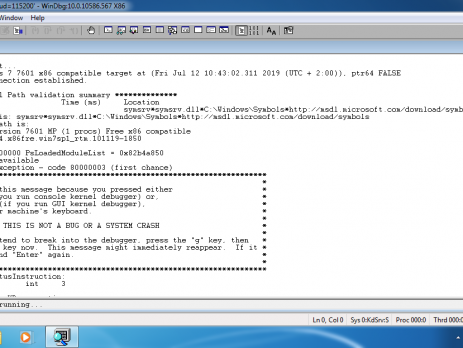
Windows Kernel Debugging & Exploitation Part1 – Setting up the lab
Recently I was thrilled with the opportunity to build a PoC for ms-14-066 vulnerability aka “winshock” (CVE-2014-6321). While that will be material for another blog post, in order to debug the vulnerability, I had to set up a lab with windows kernel mode debugging enabled. So, without any further ado, here my setup and the steps used in order to enable Windows Kernel Debug. Setup Host system: Windows 10 with VMware Workstation 15.1.0 (build-13591040) Guest systems: Windows 7 x86 ultimate sp1 (debugger) Windows...
16Nov-18
A Drone Tale
During the previous months I've been a speaker for various international conferences: Hackinbo (Italy, 26-27 May), Sec-T (Stockholm, 13-14 September) and Hacktivity (Budapest, 12-13 October) with a talk named: "A Drone Tale: All Your Drones Belongs To Us". A talk where I detailed analysed the DJI Phantom 3 model’s architecture , its attack vectors, reverse-engineered the SDK and the network protocol. I also had a specific focus section on Drones Forensics Artefacts Analysis and Methodology. Here you can find and download all...
30Aug-18
Telegram Secret Chat Bug
For whom is following me on Twitter this is not a news, yesterday I was complaining about a Telegram “Feature” in the secret chat context, while for whom doesn’t this should serve as a write-up of the bug that I have discovered (The bug is nothing fancy but something I think people should, at least, know). Telegram Secret Chat If you are not practical with the concept of Telegram’s Secret Chat: “Secret chats are meant for people who want more secrecy than the...
30Dec-17
Uncommon Phishing and Social Engineering Techniques
Sorry if you didn’t hear anything from me for a while but it was a very busy year and the new incoming one will bring a lot of news for me and for the voidsec project, I will speak about it soon in a new blog post. Today I will like to write about some uncommon techniques that I’ve used during social engineering and phishing campaign. Maybe they are not overpowered but they can be pretty useful. Behind the Scene All of these...
18Sep-17
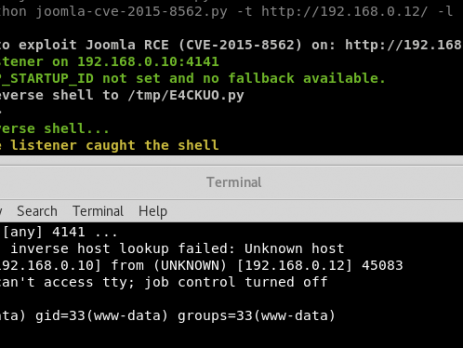
Analysis of the Joomla RCE (CVE-2015-8562)
Recently, during a penetration test I have found a vulnerable installation of the Joomla CMS. Yes, I already know that this vulnerability is quite old and that there is a ready to use Metasploit module but here is the catch: the module and other scripts available on internet weren’t working against my environment, furthermore, during the last year a lot of new vulnerabilities rely on the PHP Object Injection and Serialize/Unserialize. That's the reason why I thought it was a good...
30Jun-17
Descending into Cybercrime
More than an year ago (and before crazy and scary things like WannaCry and Petya happened) I had an idea for a research about the darkest shade of wearing a black hat, by the mean of getting some piece of information and statistics and write an analysis. Not a technical one, but something more like a financial analysis of the cybercrime business model and now I’m going to publish the results (it's even more present now than an year ago...). First...
13Jan-17
Hacking the DJI Phantom 3
Finally, during Christmas time, I had some spare time to play with my flying beast; I’m speaking about trying to hack my DJI Phantom 3. It was my first time that I operate with drones or similar embedded system and at the beginning I didn’t have any clue about how I could interact with it. The Phantom 3 comes with an aircraft, controller and an Android/iOS app. Let’s start from the beginning: As a first step, I have analysed the protocols, the connection between...
19May-16
The Curse of the Antivirus Solution
This is the main article for the VirIT Explorer Local Privilege Escalation Exploit's, if you are not interested in the methodology and the story behind this vulnerability you can directly jump to the end and reach the exploit section. As a penetration tester I've realized that Antivirus Solutions are often insecure, they can be easily bypassed and they do not fully protect your system; sometimes they also make you more vulnerable and this is the case. I will always recommend AV as...
4May-16