11Aug-20
13May-20
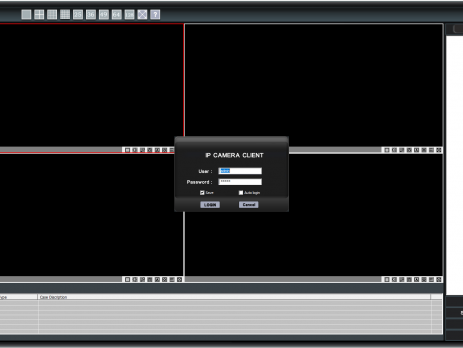
A tale of a kiosk escape: ‘Sricam CMS’ Stack Buffer Overflow
TL;DR: Shenzhen Sricctv Technology Sricam CMS (SricamPC.exe) <= v.1.0.0.53(4) and DeviceViewer (DeviceViewer.exe) <= v.3.10.12.0 (CVE-2019-11563) are affected by a local Stack Buffer Overflow. By creating a specially crafted "Username" and copying its value in the "User/mail" login field, an attacker will be able to gain arbitrary code execution in the context of the currently logged-in user. Please Note: by default, Sricam CMS requires elevation and runs in High Integrity mode; exploitation of the above software will result in a compromise of...
8Apr-20
Tabletopia: from XSS to RCE
During this period of social isolation, a friend of mine proposed to play some online "board games". He proposed “Tabletopia”: a cool sandbox virtual table with more than 800 board games. Tabletopia is both accessible from its own website and from the Steam’s platform. While my friends decided to play from their browser, I’ve opted for the Steam version. We joined a room and started a game; at one point we were messing around with some in-game cards when , for no...
2Apr-20
SLAE – Assignment #7: Custom Shellcode Crypter
Assignment #7: Custom Shellcode Crypter Seventh and last SLAE’s assignment requires to create a custom shellcode crypter. Since I had to implement an entire encryption schema both in python as an helper and in assembly as the main decryption routine, I've opted for something simple. I've chosen the Tiny Encryption Algorithm (TEA) as it does not require large IV or SBOX initialization vectors (adding a huge overhead to my shellcode's decoding routine), because it's tiny and not too complex to re-implement. As always,...
2Apr-20
SLAE – Assignment #6: Polymorphic Shellcode
Assignment #6: Polymorphic Shellcode Sixth SLAE’s assignment requires to create three different (polymorphic) shellcodes version starting from published Shell Storm's examples. I've decided to take this three in exam: http://shell-storm.org/shellcode/files/shellcode-752.php - linux/x86 execve ("/bin/sh") - 21 bytes http://shell-storm.org/shellcode/files/shellcode-624.php - linux/x86 setuid(0) + chmod("/etc/shadow",0666) - 37 bytes http://shell-storm.org/shellcode/files/shellcode-231.php - linux/x86 open cd-rom loop (follows "/dev/cdrom" symlink) - 39 bytes As always, all the code is also available on GitHub. Stay updated, join VoidSec's Telegram Channel: https://t.me/voidsec_updates execve ("/bin/sh") Original: ; http://shell-storm.org/shellcode/files/shellcode-752.php xor ecx, ecx mul ecx push ecx push 0x68732f2f ...
26Mar-20
SLAE – Assignment #5: Metasploit Shellcode Analysis
Assignment #5: Metasploit Shellcode Analysis Fifth SLAE’s assignment requires to dissect and analyse three different Linux x86 Metasploit Payload. Metasploit currently has 35 different payloads but almost half of it are Meterpreter version, thus meaning staged payloads. I’ve then decided to skip meterpreter payloads as they involve multiple stages and higher complexity that will break libemu graph generation (which I find very useful to better explain shellcode’s operations). In this blog we are going to analyse the following shellcodes: linux/x86/shell_find_tag linux/x86/shell_find_port linux/x86/shell/bind_nonx_tcp As always,...
17Mar-20
SLAE – Assignment #4: Custom shellcode encoder
Assignment #4: Custom Shellcode Encoder As the 4th SLAE’s assignment I was required to build a custom shellcode encoder for the execve payload, which I did, here how. Stay updated, join VoidSec's Telegram Channel: https://t.me/voidsec_updates Encoder Implementations I’ve decided to not relay on XORing functionalities as most antivirus solutions are now well aware of this encoding schema, the same reason for which I’ve skipped ROT13 and other “rotating” encoding. I thought of using some multiple weird shifting schema but that would have had a...
20Feb-20
SLAE – Assignment #3: Egghunter
Assignment #3: Egghunter This time the assignment was very interesting, here the requirements: study an egg hunting shellcode and create a working demo, it should be configurable for different payloads. As many before me, I’ve started my research journey with Skape’s papers: “Searching Process Virtual Address Space”. I was honestly amazed by the paper content, it’s not only very well written and explained but it ‘s mind-blowing. Understanding why and how egg hunter shellcode should be crafted in such tailored way was...
22Jan-20
SLAE – Assignment #2: Reverse TCP Shell
Assignment #2: Reverse TCP Shell Create a shell_reverse_tcp shellcode that connects back to an IP address, on a specific a port and execute a shell. The IP address and port number should be easy configurable. Again, instead of going for the path of writing a C TCP reverse shell from scratch, I decided to generate a raw Metasploit payload and analyze it with libemu. Analyzing the Shellcode All the code is also available on GitHub. This time the analysis will be a lot shorter due...
9Jan-20