11Aug-20
18Sep-17
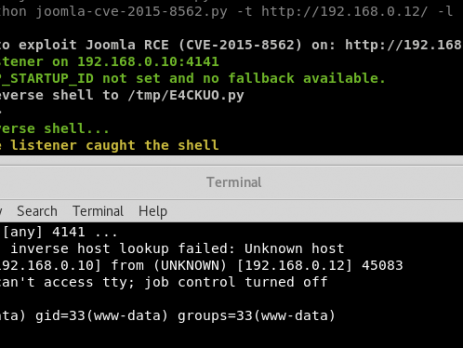
Analysis of the Joomla RCE (CVE-2015-8562)
Recently, during a penetration test I have found a vulnerable installation of the Joomla CMS. Yes, I already know that this vulnerability is quite old and that there is a ready to use Metasploit module but here is the catch: the module and other scripts available on internet weren’t working against my environment, furthermore, during the last year a lot of new vulnerabilities rely on the PHP Object Injection and Serialize/Unserialize. That's the reason why I thought it was a good...
19May-16
The Curse of the Antivirus Solution
This is the main article for the VirIT Explorer Local Privilege Escalation Exploit's, if you are not interested in the methodology and the story behind this vulnerability you can directly jump to the end and reach the exploit section. As a penetration tester I've realized that Antivirus Solutions are often insecure, they can be easily bypassed and they do not fully protect your system; sometimes they also make you more vulnerable and this is the case. I will always recommend AV as...
4May-16
ImageTragick PoC
ImageMagick Is On Fire — CVE-2016–3714 There are multiple vulnerabilities in ImageMagick, a package commonly used by web services to process images. One of the vulnerabilities can lead to remote code execution (RCE) if you process user submitted images. The exploit for this vulnerability is being used in the wild. A number of image processing plugins depend on the ImageMagick library, including, but not limited to, PHP’s imagick, Ruby’s rmagick and paperclip, and nodejs’s imagemagick. For more information about this vulnerability visit: https://imagetragick.com/ or this...
21Apr-16
Phorum – Full Disclosure
Reporter VoidSec Security Team Advisory VoidSec-16-002 Date of contact 03-03-16 2nd date of contact 16-03-16 3rd date of contact 04-04-16 Vendor last reply 03-03-16 Date of public disclosure 21-04-16 Product Phorum Open Source PHP Forum Software Version 5.2.20 Download the Report [EN] Introduction The purpose of the present project is to assess the security posture of some important aspects of Phorum Forum Software. Phorum is open source forum software with a penchant for speed. Phorum's very flexible hook and module system can satisfy every web master's needs. During the web application security assessment for Phorum, VoidSec assessed the following systems using...
19Apr-16
LinkedIn – CSV Excel formula injection
We are proud to publish an undisclosed vulnerability affecting LinkedIn and in particular its "CSV Export" function. Following our Vulnerability Disclosure Policy Agreement, LinkedIn Security Team has been informed about this specific issue and this vulnerability will be published without a working PoC. LinkedIn's users can exports all their connections into a CSV file, that due to some missing filters (escaping output), could allows an attacker to execute a command on the user machine. An attacker can create a LinkedIn profile embedding a...
13Apr-16
Avactis – Full Disclosure
Advisory: VoidSec-16-001 Date of contact: 19-01-16 2nd date of contact: 23-01-16 Vendor reply: N/A Date of public disclosure: 12-04-16 Product: Avactis PHP Shopping Cart Version: 4.7.9.Next.47900 Vendor: Avactis Download the Report [EN] Introduction Avactis is an open source ecommerce Shopping Cart software. The purpose of the present project is to assess the security posture of some important aspects of Avactis PHP Shopping Cart. The activity is performed through Web Application Penetration Test using Grey Box approach. Vulnerabilities: Spreading of Files with Malicious Extensions on Upload New Design and Execution in some circumstances Non-Admin PHP Shell...
1Oct-15
Deep Web & Hacking Communities
Qualche mese fa sono stato intervistato da Pierluigi Paganini per Infosec Institute riguardo l’argomento: Hacking Communities in the Deep Web. Vi propongo quindi la sessione di Q&A tradotta in Italiano, l’articolo originale è ben più vasto di questo piccolo “recap” e ne consiglio la lettura. Si sente spesso parlare di Deep Web, cosa s’intende con questo termine? Il Deep Web è l’insieme di tutti i contenuti internet non indicizzati dai motori di ricerca e pertanto difficilmente raggiungibili dagli utenti standard. Sovente viene utilizzato...
18Jun-15
Minds.com – Full Disclosure
Advisory: VoidSec-15-002 Disclosure date: June18, 2015 Vendor: Minds.com Advisory sent: June 17, 2015 Paolo Stagno ( aka voidsec – [email protected] ) Luca Poletti ( aka kalup – [email protected] ) Download the Report [EN] Introduction In those last days a new social network called minds is getting attention over the internet, it aims to give transparency and protection to user data. Thanks to those last two points the new site has attracted the support of online activists including the hacking collective Anonymous. We have then decided to give a look to that amazing platform,...
7Mar-15