20Jan-22
16Dec-21
Merry Hackmas: multiple vulnerabilities in MSI’s products
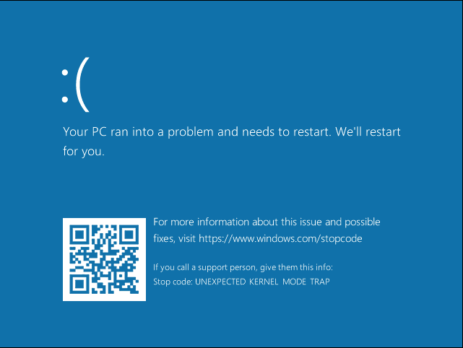
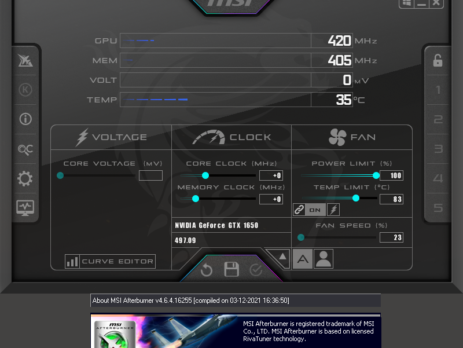
This blog post serves as an advisory for a couple of MSI’s products that are affected by multiple high-severity vulnerabilities in the driver components they are shipped with. All the vulnerabilities are triggered by sending specific IOCTL requests and will allow to: Directly interact with physical memory via the MmMapIoSpace function call, mapping physical memory into a virtual address user-space. Read/write Model-Specific Registers (MSRs) via the __readmsr/__writemsr functions calls. Read/write 1/2/4 bytes to or from an IO port. An attacker could exploit...
5May-21
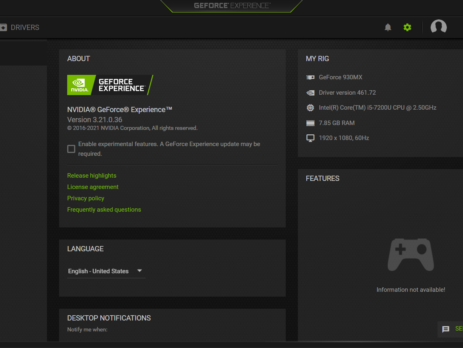
CVE‑2021‑1079 – NVIDIA GeForce Experience Command Execution
NVIDIA GeForce Experience (GFE) v.<= 3.21 is affected by an Arbitrary File Write vulnerability in the GameStream/ShadowPlay plugins, where log files are created using NT AUTHORITY\SYSTEM level permissions, which lead to Command Execution and Elevation of Privileges (EoP). NVIDIA Security Bulletin – April 2021 NVIDIA Acknowledgements Page This blog post is a re-post of the original article “Chaining Bugs: CVE‑2021‑1079 - NVIDIA GeForce Experience (GFE) Command Execution” that I have written for Yarix on YLabs. Introduction Some time ago I was looking for...
11Aug-20